Random Number Generators and Information Security
From Computing and Software Wiki
(Difference between revisions)
(→References) |
|||
| Line 18: | Line 18: | ||
== Conclusion == | == Conclusion == | ||
== References == | == References == | ||
| + | 1. Bishop, M. 2004. Introduction to Computer Security. Prentice Hall PTR. | ||
| + | 2. Wikipedia. 2007. Retrieved November 27, 2007. <http://wikipedia.org> | ||
| + | 3. Haahr, M. 2007. Random.org. Retrieved November 27, 2007. <http://www.random.org> | ||
| + | |||
== See Also == | == See Also == | ||
== External Links == | == External Links == | ||
--[[User:Caoff|Caoff]] 19:00, 1 December 2007 (EST) | --[[User:Caoff|Caoff]] 19:00, 1 December 2007 (EST) | ||
Revision as of 00:29, 2 December 2007
Contents |
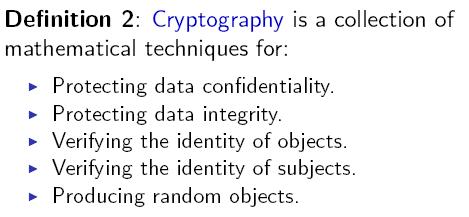
Relevance to Information Security
Vulnerability
Two Kinds of Randomness
True Randomness
Physical Methods
Examples
Pros and Cons
Pseudo-Randomness
Computational Methods
Examples
Pros and Cons
Verdict
Conclusion
References
1. Bishop, M. 2004. Introduction to Computer Security. Prentice Hall PTR. 2. Wikipedia. 2007. Retrieved November 27, 2007. <http://wikipedia.org> 3. Haahr, M. 2007. Random.org. Retrieved November 27, 2007. <http://www.random.org>
See Also
External Links
--Caoff 19:00, 1 December 2007 (EST)