Payment Card Industry Data Security Standard
From Computing and Software Wiki
The Payment Card Industry Data Security Standard (PCI DSS) is a security document created by the Payment Card Industry Security Standards Council (PCI SSC). To make the explanation of the PCI DSS a bit more interesting, I will be presenting it as an Industry Wide security do
Contents |
Security System Life Cycle
Threats
The main threat to the Payment Card Industry as a whole is more of a threat to the card holders than the industry itself. The card holders are taking a chance whenever they use their credit cards to make a purchase. This threat is not only present when purchasing online, but also when purchasing in stores. The threat originates from a lack of industry wide standards on how card holder information should be stored, processed or transmitted.
This security threat directly affects the Payment Card Industry because if cardholders don't trust that their information is secure, then they will not use their credit cards and hence the Payment Card Vendors loose business. This is why the Payment Card Industry is moving forward with their industry wide standard for security, the Payment Card Industry Data Security Standard.
Policy
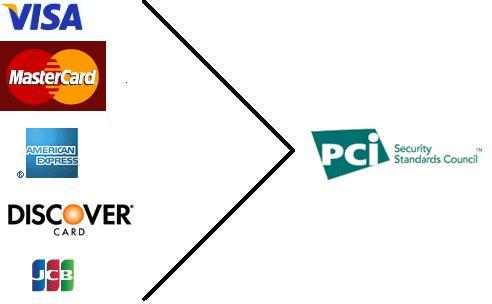
Before December 14th 2004, the 5 major Payment Card companies (Visa, Mastercard, American Express, Discover and JCB (Japan Credit Bureau)) each had their own set of Information Security Standards. This meant that retailers had 5 different security policies to comply to. After December 14th 2004, these 5 brands of cards collaborated to create the Payment Card Industry Security Standards Council (PCI SSC). The purpose of this council is to align the goals of each of the Payment Card companies an industry wide security policy for merchants to follow.
Security System Development
Requirements Specifications
Design/Implementation
Operation and Maintenance
Summary
References
See Also
Electronic Voting Systems
Social engineering
Piggybacking
Identity Theft
The Mitnick attack
Security and Storage Mediums
Operating Systems Security
Honeypot