Honeypot
From Computing and Software Wiki
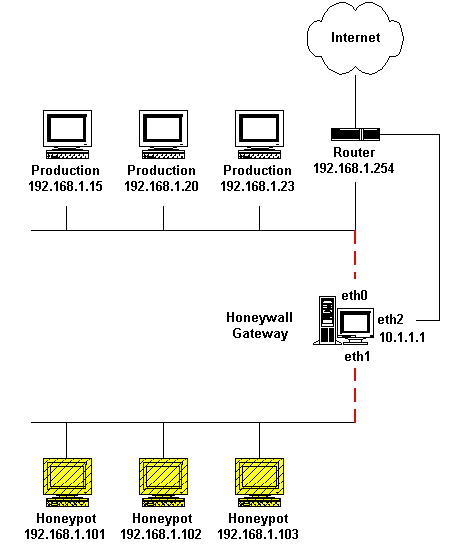
In computing terminology, a Honeypot is a closely monitored network decoy that serves several purposes. It can provide early warning about a new attack or exploitation trends, can distract adversaries from other more valuable resources on a network, or allow a detailed examination of adversaries during and after a honeypot has been exploited.
A Honeypot usually serves as a surveillance and early warning tool. It doesn't fix a single problem, but is a highly flexible security tool that has different applications for security. It has multiple uses including prevention, detection and information gathering. Honeypots all have the same concept that they don't have any production or authorized activity. A Honeypot should not see any legitimate traffic and can be surmised that it will only capture malicious or unauthorized activity. After being deployed in a network, a honeypot should not affect critical network services and applications. Its value as a security resource lies in being probed, attacked or compromised.
A Honeypot can also carry certain risks to a network and should be handled with care. If it is not properly looked after or walled off, an attacker can use it to break into another system.
Contents |
Types of Honeypots
References
See also
External Links
--Colbyl2 18:42, 1 December 2007 (EST)