Electronic Voting Systems
From Computing and Software Wiki
(→Insider Attacks) |
(→Insider Attacks) |
||
| Line 43: | Line 43: | ||
Insider attacks can be caused by software developers, Poll workers, or other Election officials who are aware of the inner workings of the DRE Machine and how it is implemented. | Insider attacks can be caused by software developers, Poll workers, or other Election officials who are aware of the inner workings of the DRE Machine and how it is implemented. | ||
| + | |||
<br>'''Ex. 1.''' A software developer can change a single line of code to give 10% of all votes to a desired party. | <br>'''Ex. 1.''' A software developer can change a single line of code to give 10% of all votes to a desired party. | ||
<br>'''Ex. 2.''' A programmer working on the system can change the ordering of candidates in the 'ballot definition' file but keep the original order in the 'result file'; therefore | <br>'''Ex. 2.''' A programmer working on the system can change the ordering of candidates in the 'ballot definition' file but keep the original order in the 'result file'; therefore | ||
Revision as of 18:16, 7 December 2007
An Electronic Voting System is an innovative new method of distributing, voting, collecting and tabulating ballots through the use of computer technology.
The software implementations which are input into this technology expand every day to improve
security and integrity of the results.
Contents |
Electronic Voting Systems
DRE Machines
DRE (Direct Recording Electronic)
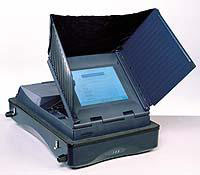
A DRE machine is a recent implementation of a fully self-operated computer voting system.
DRE's are user-friendly and time-efficient which makes them an attractive alternative to traditional pen-and-paper voting. A DRE machine consists of a user screen
for information and ballot display, a keypad involving buttons or a touchscreen, and other assisting tools such as head-phones for the handicapped.
DRE's have been implemented worldwide but most frequently used in countries such as Brazil, India and United States.
To access a DRE machine, a voter must be provided with a Voter Authentication Card (SmartCard or another type of Memory Card) by an Election Official. The Voter card
becomes automatically deactivated by the DRE once a vote is fully cast.
Optical Scan
Optical Scanning machines were introduced shortly after the Punch Card system, incorporating paper ballots with computer technology. There are two common Optical Scanning Machines
used in todays elections, Marksense and the Digital Pen.
Marksense is a system originally developed in Australia. Using a dark marker, a voter shades in their selection on the paper ballot, once completed the paper ballot is run through an optical scanning
machine which uses 'dark mark' logic to select the correct vote. The votes are automatically tabulated using the machine but may also be tabulated manually using the hard copy ballots.
A Digital Pen is a similar version to Marksense except the pen communicates with the paper ballot and knows at all times its location on the ballot. A small camera may also be built within
the pen to keep track of the votes. At the end of the voting session, the pen is taken for vote tabulation and the hard copy ballots are kept for recounts.
Internet Voting
Internet voting has been widely used in private elections where anonymity, data integrity and tempering assurance are handled with lower standards than private elections.
Voting over the internet can be done remotely (open network) or from a poll site. Implementation of e-voting has been recorded across the UK, US, Canada, France, Estonia & Switzerland.
To improve voter authentication, secrecy and security, technologies such as Electronic Authentication and computer Security are used.
Electoral Fraud
Insider Attacks
DRE Machines
Insider attacks can be caused by software developers, Poll workers, or other Election officials who are aware of the inner workings of the DRE Machine and how it is implemented.
Ex. 1. A software developer can change a single line of code to give 10% of all votes to a desired party.
Ex. 2. A programmer working on the system can change the ordering of candidates in the 'ballot definition' file but keep the original order in the 'result file'; therefore
the reordered list will appear on the DRE screen and voters will unwillingly cast votes for wrong candidates.
Internet
Since there is less human involvement over internet voting, the only serious insider attack may be caused by Election officials who are in charge of the networking, operating system
and hardware.