Payment Card Industry Data Security Standard
From Computing and Software Wiki
The Payment Card Industry Data Security Standard (PCI DSS) is a security document created by the Payment Card Industry Security Standards Council (PCI SSC). To make the explanation of the PCI DSS a bit more interesting, I will be presenting it as an Industry Wide security do
Contents |
Terms Used In This Article
- PCI Payment Card Industry: A Payment Card is any "card" form of payment. This can cover everything from credit cards to debit cards. The Payment Card Industry consists of all the companies which make up the many different brands of payment cards in use today. (ie Visa, Mastercard, ect..)
- PCI DSS Payment Card Industry Data Security Standard
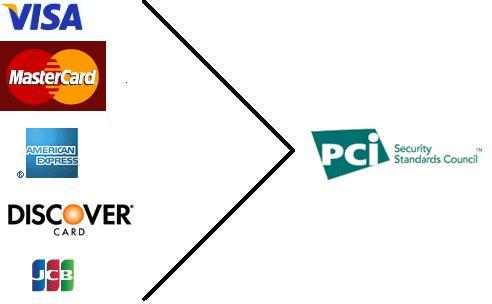
- PCI SSC Payment Card Industry Security Standards Council: A council made up of Visa, Mastercard, American Express, Discover and JCB (Japan Credit Bureau) created in order to align their individual security goals into one document - the PCI DSS.
- Card Holder: Any customer of a Payment Card company.
- Merchant: Any company which accepts Payment Cards as a form of payment.
Security System Life Cycle
Threats
The main threat to the Payment Card Industry as a whole is more of a threat to the card holders than the industry itself. The card holders are taking a chance whenever they use their credit cards to make a purchase. This threat is not only present when purchasing online, but also when purchasing in stores. The threat originates from a lack of industry wide standards on how card holder information should be stored, processed or transmitted.
This security threat directly affects the Payment Card Industry because if cardholders don't trust that their information is secure, then they will not use their credit cards and hence the Payment Card Vendors loose business. This is why the Payment Card Industry is moving forward with their industry wide standard for security, the Payment Card Industry Data Security Standard.
Policy
Before December 14th 2004, the 5 major Payment Card companies (Visa, Mastercard, American Express, Discover and JCB (Japan Credit Bureau)) each had their own set of Information Security Standards. This meant that retailers had 5 different security policies to comply to. After December 14th 2004, these 5 brands of cards collaborated to create the Payment Card Industry Security Standards Council (PCI SSC). The purpose of this council is to align the goals of each of the Payment Card companies an industry wide security policy for merchants to follow.
Security System Development
Requirements Specifications
An overview of the list of requirements needed to maintain Payment Card Industry Data Security Standard (PCI DSS) compliance is available here About the PCI Data Security Standard (PCI DSS). The full list of requirements is available here: Download the PCI DSS. Below is the summarized list and an explaination of what each item means. There are 12 major requirements which can be broken up into 6 categories.
Build and Maintain a Secure Network
1.)Install and maintain a firewall configuration to protect cardholders' data
2.)Do not use vendor-supplied defaults for system password and other security parameters
- This set of requrements is meant to keep any network of computers which contain Card Holder information in a secure state
Protect Cardholder Data
3.)Protect stored cardholder data
- This requirement is meant to protect the card holder data while it is stored on merchant computers
4.)Encrypt transmission of cardholder data across open, public networks
- This requirement is meant to protect cardholder data when it might be necessary to transmit it accross a public network (ie when contacting the Payment Card server)
Maintain a Vulnerability Management Program
5.)Use and regularly update anti-virus software
- This requirement is meant to ensure that all merchants do take advantage of some form of anti-virus software.
6.)Develop and maintain secure systems and applications
- This requirement is meant to put security as a top priority during the development of software. This is an important requirement because many times when software is being designed, security is tacked on as an afterthought. By at least making developers aware of security as being a requirement of their software, this ensures better quality of any security mechanisms built into the software.
Implement Strong Access Control Measures
7.)Restrict access to cardholder data by business need-to-know
- This requirement is meant to ensure that only people who need to know about cardholder data have access to it. This is similar to the principle of least privilege.
8.)Assign a unique ID to each person with computer access
- This requirement is meant to add a level of accountability to all users on the system. If each user has their own unique ID on the merchant's system, then actions can be tracked on linked to the person who did them.
9.)Restrict physical access to cardholder data
- This requirement is meant to extend the coverage of the PCI DSS to any form of Card Holder data which may not be on a computer. Hence, the PCI DSS is extended to cover not only digital information but also physical coppies of the information. However, this does not prevent the threat of customer data being stolen entirely. There is nothing to prevent an employee from copying down information with a pencil and paper. Though this is a problem, it is partially alleviated by requirement 7: Restrisct access to cardholder data by business need-to-know. If only a small number of employees can access the Card Holder data, then it is much easier to track down who may have stolen Card Holder data if there is a security breech from the inside.
Regularly Monitor and Test Networks
10.) Track and monitor all access to network resources and cardholder data
- This requirement is designed to catch any unauthorized accesses to cardholder data. If an anomoly is detected, then the system should be able to detect it and steps should be taken to fix the problem
11.) Regularly test security systems and processes
- This requirement is meant to ensure that merchants don't just set and forget their security systems. It reminds them that security is a fulltime job and must constantly be maintaned.
Maintain an Information Security Policy
12.) Maintain a policy that addresses information security
- Though this may seem a bit redundant, this is an important requirement. It means that every merchant that deals with Cardholder Data must have their own security policy as well in order to protect cardholder data.
Design/Implementation
There is no design or implementation specified in the PCI DSS. This is because the application of this security policy is so broad that it is impossible to have one design that will work for every company. For example Soney, which may handle millions of transactions a year, will need a different implementatino than a small "mom and pop" company, who may handle only a few hundred transactions a year. However, requirements must still be met to some degree depending on the volume of Payment Card transactions which occur per given merchant. This makes the PCI DSS sound rather weak. However, there is a way which the Payment Card Industry Security Standards Council can keep track of whether or not the requirements are being met. This is through the use of QSA's and ASV's.
- Qualified Security Assessors (QSA's) are companies who have been approved by the PCI Security Standrads Council to assess the compliance of merchants to the PCI DSS. The way the PCI Security Standards Council does this is through a certification program. This requires not only the company to be certified, but also all of it's employees to be certified on a yearly bases.
- Approved Scanning Vendors (ASV's) are companies who are approved by the PCI Security Standards Council to assess merchants' networks for security vulnerabilities. They accomplish this by simulating both normal and abnormal processes on the merchants networks. Again, ASV's must also be certified by the PCI Security Standards Council on a yearly basis.
Operation and Maintenance
Summary
References
- Template:NotePCI SSC
See Also
Electronic Voting Systems
Social engineering
Piggybacking
Identity Theft
The Mitnick attack
Security and Storage Mediums
Operating Systems Security
Honeypot