Steganography and Digital Watermarking
From Computing and Software Wiki
Steganography and Digital Watermarking are both forms of information hiding where the context can be viewed as keeping the information a secret or making the information subtle respectively. Both these methods have been around for a long time, at least several centuries, however they have only gained worldwide popularity in the digital world since roughly the mid 1990s. With new technologies constantly emerging, these two methods have been used to prevent theft, prevent plagiarism, track, and hide secrets.
Contents |
History
Test
Applications
Steganography and digital watermarking can be broken down into four different subcategories in which the existence of the technique is either known or unknown to the public.
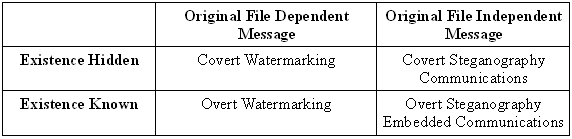
Covert watermarking is embedding a watermark related to the recipient of each copy of the file, but unaware that the watermark exists. Thus, if the file is leaked to third parties, the recipient who leaked the file can be traced. Covert steganography is embedding data unrelated to the original work. An overt watermark is when the presence of the watermark is known to others besides the creators, whether visually or told of the watermark. Overt steganography is similar to covert steganography in terms of the hidden information is unrelated to the signal in which it is embedded in. However with overt steganography, the information is only hidden to certain parties but visible to others, example timestamps.
Knowing the subcategories allows for the following possible applications for both steganography and digital watermarking. Some applications may use both techniques depending on the function required.
Steganography
Some applications of steganography are:
- Protection of Data Alteration
- Confidential Communication
- Media Database Systems
- Access Control
Watermarking
Some applications that use digital watermarking are:
- Broadcast Monitoring
- Owner Identification
- Proof of Ownership
- Transaction Tracking
- Content Authentication
- Copy Control
- Device Control
- Legacy Enhancement
