Man in the Middle Attack
From Computing and Software Wiki
| Line 32: | Line 32: | ||
==References== | ==References== | ||
| - | + | #A Weakness in the 4.2BSD Unix TCP/IP Software, Robert T. Morris, AT&T Bell Laboratories, February 1985 <BR> | |
| - | + | #http://www.csl.sri.com/users/ddean/papers/spoofing.pdf <BR> | |
| - | + | #http://www.contentverification.com/man-in-the-middle/ <BR> | |
---- | ---- | ||
--[[User:Heifetj|Heifetj]] 03:17, 6 April 2009 (EDT) | --[[User:Heifetj|Heifetj]] 03:17, 6 April 2009 (EDT) | ||
Revision as of 09:20, 6 April 2009
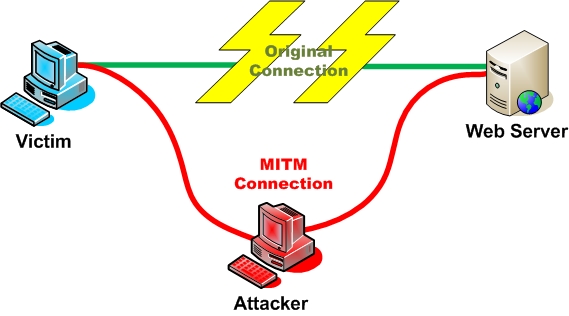
Man in the Middle Attacks (sometimes MITM) are attacks where the attacker intercepts communication between two parties, forwarding the communication as if the attacker were not present. The name is derived from the popular game Man in the Middle. It is also referred to as a fire-brigade or bucket brigade attack based on the method for putting out a fire. Lastly it is referred to as a Janus attack in reference to the roman two-headed god of gates.
Contents |
Example
Alice sends a communication to Bob, which is intercepted by an attacker, and then forwarded on to Bob. Bob then replies to Alice which is also intercepted by the attacker, and then forwarded to Alice.
Prominent Attacks
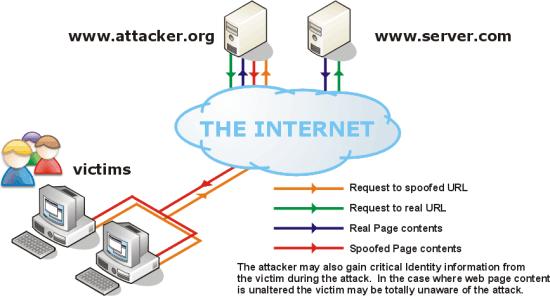
Historically, several different man in the middle attacks have been described. Perhaps the earliest reference was a paper showing the possibility of IP spoofing in BSD Linux.[1] A more recent and famous example is The Mitnick attack, a man in the middle attack taking advantage of the structure of IP to establish the trusted connections. Another common man in the middle attack is IP spoofing, where victims have all their web traffic re-routed through the attacker.[2]
Another common attack is DNS Cache Poisoning, an attack where a user's DNS cache is overwritten, directing their requests through the attacker instead of the correct host.[3]
Attacking Tools
Defences
Beyond Computing
See Also
Information Security Topics:
- IP Spoofing
- Piggybacking
- Phishing
- Operating Systems Security
- Information security awareness
- Network stack (dode) - attack patterns on each layer & how to defend it
External Links
References
- A Weakness in the 4.2BSD Unix TCP/IP Software, Robert T. Morris, AT&T Bell Laboratories, February 1985
- http://www.csl.sri.com/users/ddean/papers/spoofing.pdf
- http://www.contentverification.com/man-in-the-middle/
--Heifetj 03:17, 6 April 2009 (EDT)