Malware
From Computing and Software Wiki
| Line 6: | Line 6: | ||
==Purpose== | ==Purpose== | ||
| - | There are numerous reasons why malware is written. | + | There are numerous reasons why malware is written, but it usually involves one illicit purpose or another. The following are some generic purposes where most malware falls under. |
=====Obtaining sensitive information===== | =====Obtaining sensitive information===== | ||
| Line 29: | Line 29: | ||
=====Hidden===== | =====Hidden===== | ||
Hidden malware's key feature is its ability to hide itself within a computer system. | Hidden malware's key feature is its ability to hide itself within a computer system. | ||
| - | * Trojan horses | + | * [http://en.wikipedia.org/wiki/Trojan_horse_(computing) Trojan horses] |
| - | * Root kits | + | * [http://www.cas.mcmaster.ca/wiki/index.php/Rootkits Root kits] |
=====Deceptive===== | =====Deceptive===== | ||
The most bothersome, deceptive malware preys on users who may not be as tech-savvy as others. | The most bothersome, deceptive malware preys on users who may not be as tech-savvy as others. | ||
Revision as of 20:45, 11 April 2009
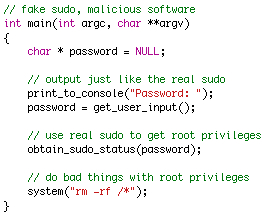
Malicious software (malware) encompasses a broad range of software typically designed to covertly operate and deceive users to hide its actual intended purpose. It can be used as a catch-all phrase for software that has been programmed for malicious purposes intentionally, software such as viruses, worms, spyware, and botnets. Its purpose can vary, but typically it is used to gather information, generate profit, cause harm or data loss, or it could have no real purpose at all.
Contents |
History
Before computers were accessible to the general public, malware was not an overwhelming threat. Starting sometime in the 1970's computers became somewhat more common, and as a direct result, so did malicious software. At this time, viruses started to appear on networks such as ARPANET, gaining popularity into the 1980's with the explosion of person computers. Early malware was typically less of a threat, created by programmers who were trying to prank other users, rather than the typical malware created for todays society.
Purpose
There are numerous reasons why malware is written, but it usually involves one illicit purpose or another. The following are some generic purposes where most malware falls under.
Obtaining sensitive information
Malware can be used to gather sensitive information. With the recent expansion of mobile computing, malware authors are targeting mobile computers, such as smart phones, because of the amount of sensitive information contained within them.
Obtaining financial returns
Malware can be used to generate illicit revenues, usually by hijacking ad revenues or using previously mentioned sensitive information to the benefit of the malware user.
Cause harm or data loss
The most common use of all, malware can be used to cause damage to a computer system in one way or another.
No real purpose
Sometimes malware authors create software that has no intended purpose what so ever.
Types with examples
Typically malware is composed from a combination of several distinct types.
Infectious
Infectious malware gets its name from its method of propagation. Similar to biological viruses, infectious malware spreads itself by self-replicating on some medium, whether it be a computer network or computer system.
Hidden
Hidden malware's key feature is its ability to hide itself within a computer system.
Deceptive
The most bothersome, deceptive malware preys on users who may not be as tech-savvy as others.
- Adware
- Spyware
Prevention
- Linux lol