Network firewall
From Computing and Software Wiki
(→Simple packet filtering: IP or filtering Firewall) |
(→Simple packet filtering: IP or filtering Firewall) |
||
| Line 59: | Line 59: | ||
===Simple packet filtering: IP or filtering Firewall=== | ===Simple packet filtering: IP or filtering Firewall=== | ||
An IP filtering firewall works at the simple IP packet level. It is designed to control the flow of data packets based on their header information (Source, destination, port, and packet type).[2:50] | An IP filtering firewall works at the simple IP packet level. It is designed to control the flow of data packets based on their header information (Source, destination, port, and packet type).[2:50] | ||
| - | [[Image:IpHeader.gif|thumb|right| | + | [[Image:IpHeader.gif|thumb|right|500px|Figure 2 - Typical Ipv4 Packet Header]] |
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
| - | + | ||
A traditional firewall, like a simple router, is generally make their decision based on the source, destination addresses, and port in individual IP packets. Modern simple packet-filtering firewalls have become increasingly sophisticated and maintain internal information about the state of connections passing through them, the contents of some of the data steam, and so on | A traditional firewall, like a simple router, is generally make their decision based on the source, destination addresses, and port in individual IP packets. Modern simple packet-filtering firewalls have become increasingly sophisticated and maintain internal information about the state of connections passing through them, the contents of some of the data steam, and so on | ||
Revision as of 01:44, 11 April 2009
Network Firewall is now considered as a first line of defense in the form of a barrier against outside attacks, which is installed on computers connect to internet. In general Firewall prevents the dangers of Internet from spreading to your internal network. It more like a moat of a medieval castle that a firewall in a modern building. It serves multiple purposes [1:21]:- It restricts people to entering at a carefully controlled point.
- It prevents attackers from getting close to your other defenses.
- It restricts people to leaving at a carefully controlled point.[1:21]
In practice,a firewall is a collection of hosts, routers, and other hardware that designed to prevent unauthorized electronic access between two parts of a network. It is also a device or set of devices configured to permit, deny, encrypt, decrypt, or proxy all computer traffic between different security domains based upon a set of rules and other criteria.[3]
Firewalls can be implemented in both hardware and software, or a combination of both. Firewalls are frequently used to prevent unauthorized Internet users from accessing private networks connected to the Internet, especially intranets. All messages entering or leaving the intranet pass through the firewall, which examines each message and blocks those that do not meet the specified security criteria.[3]
Contents |
Why Firewall
The Internet is marvelous technological advance that provides access to information, and the ability to publish information, in revolutionary ways. But it's also a major danger that provides the ability to pollute and destroy information in revolutionary ways. For this reason, no matter what kind of information you put on Internet, you may always try to protect:
- Your Data?
- Secrecy: accessibility for a certain group of people
- Integrity: no data change by others
- Availability: always able to use it by you or by a group of people who have the permit.
- Your Resources? Your computer cycle and storage space.
- Your Reputation? No one should appear on the Internet with your identity. [1:7]
if you answer YES to any of above, then Network Firewall is the solution you needed.
What is Firewall
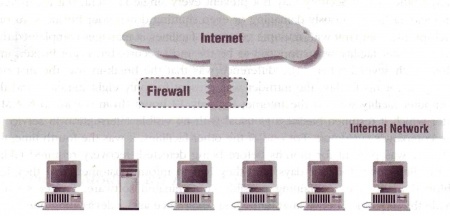
As figure 1 shows, a Firewall is a box/device between two connected networks, it has the following definitions:
- A Firewall is an integrated collection of security measures designed to prevent unauthorized electronic access to a networked computer system.[3]
- A Firewall is a device or set of devices configured to permit, deny, encrypt, decrypt, or proxy all computer traffic between different security domains based upon a set of rules and other criteria.[3]
- A Firewall is a device that divide a network into parts, when some parts have distinct security needs.[1:23]
- A Firewall is a separator, a restricter, an analyzer.[1:22]
Benefits of Firewall
Generally, Firewalls are configured to protect against unauthenticated interactive logins for the outside world, most of the time, it acts like a choke point. All traffic in and out must pass through this single, narrow choke point, which provided a very easy mechanism to monitor, trace, and control information flow. Hence, Firewall is an efficient network security tool to block Intrusion, Denial of service, and Information theft. The following are the primary benefits of using a firewall:
- Protection from vulnerable service that are running on the server that may increase its vulnerability to attack
- Controlled access to site systems
- Concentrated Security
- Enhanced privacy
- Logging and statistics on network use, misuse
- Policy enforcement
- VPN
- DMZ
[2:12]
Limitations of Firewall
- Network Firewall cannot protect against attacks that don't go through the Firewall.
- example: a dial-up modem connection that allow users to dial-in to access the internal systems behind the firewall. The firewall has absolutely no way of preventing an intruder from getting in through such a modem.
- Network Firewall cannot protect against malicious insiders.
- Internal users may be blocked from sending information out by Firewall block service, but they can still download, copy the data onto disks or flash drives.
- Network Firewall cannot protect against viruses.
- Detecting a virus in a random packet of data passing through a Firewall is very difficult, as it requires:
- recognizing that the packet is part of a program
- Determine what the program should look like and its behavior.
- Determine that a change in the program is a threats to system
- Detecting a virus in a random packet of data passing through a Firewall is very difficult, as it requires:
- Network Firewall cannot protect against completely new threats.
- Firewall is designed to protect against known threats. People continuously discover new ways to attack, using previously trustworthy services, or using attacks that simply has not occurred to anyone before.
- Network Firewall cannot set itself up correctly.
- Every Firewall need some amount of configuration, as every site/private network is different, so it is impossible to use a universal firewall which will set itself up automatically. Correct configuration is absolutely essential.
[1:24]
Firewall Types
There are three types of Firewalls, as:
- Simple packet filtering: IP or filtering firewalls -- Block all but selected network traffic
- Application-layer firewall: Proxy server -- act as intermediary to make requested network connections for the user
- Stateful multilayer-inspection firewalls -- extract the relevant communication and application state information and analyze all packet communication layers.
Simple packet filtering: IP or filtering Firewall
An IP filtering firewall works at the simple IP packet level. It is designed to control the flow of data packets based on their header information (Source, destination, port, and packet type).[2:50]
A traditional firewall, like a simple router, is generally make their decision based on the source, destination addresses, and port in individual IP packets. Modern simple packet-filtering firewalls have become increasingly sophisticated and maintain internal information about the state of connections passing through them, the contents of some of the data steam, and so on
Application Firewalls: proxy servers
Stateful multilayer-inspection Firewalls
Firewall Architectures
Single-Box
Screened host
Screened subnet
Firewall Software
Simple Packet - Filter Firewall By sudhirmangla, The CodeProject.com
References
- Elizabeth D. Zwicky, Simon Cooper, and D. Brent Chapman;Building internet Firewalls, Second Edition; Published by O'Reilly & Associates, Inc. @2000; ISBN:1-56592-871-7, McMaster Thode Library: TK 5105.59.Z85 2000
- John R. Vacca, Scott R. Ellis; Firewalls, Jumpstart for Network and Systems Administrators; Elsevier digital press @2005; ISBN: 1-55558-297-4, McMaster Thode Library: TK 5105.59.V32 2005
- Firewall, Wikipedia, Accessed on April 3rd 2009 21:35.
- IPv4 Packet Header, Engineering, University of Aberdeen, Accessed on April 10th 2009 21:10
See also
External links
- Firewalls and Internet Security by Frederic Avolio, Avolio Consulting, Cisco Systems.
- History of Firewall Technologies A text file by Rik Farrow and Richard Power, Spirit.com
Time-stamped Signature
Fulx 21:16, 10 April 2009 (EDT)