Computer Network Traffic Shaping
From Computing and Software Wiki
| Line 1: | Line 1: | ||
| - | Traffic shaping (also referred to as packet shaping) is the technique of delaying and restricting certain packets traveling through a network to increase the performance of packets that have been given priority. Classes are defined to separate the packets into groupings so that they can each be shaped separately allowing some classes to pass through a network more freely than others. Traffic shapers are usually placed at the boundaries of a network to either shape the traffic going entering or leaving a network. | + | Traffic shaping (also referred to as packet shaping) is the technique of delaying and restricting certain packets traveling through a network to increase the performance of packets that have been given priority. Classes are defined to separate the packets into groupings so that they can each be shaped separately allowing some classes to pass through a network more freely than others. Traffic shapers are usually placed at the boundaries of a network to either shape the traffic going entering or leaving a network. Traffic shaping does not actually speed up a networks total thoughput. It is a tool used to help manage a network's resources. |
| Line 8: | Line 8: | ||
===Leaky bucket=== | ===Leaky bucket=== | ||
| - | |||
| - | |||
[[Image:LeakyBucket.jpg|thumbnail|right|250px|Leaky Bucket[4]]] | [[Image:LeakyBucket.jpg|thumbnail|right|250px|Leaky Bucket[4]]] | ||
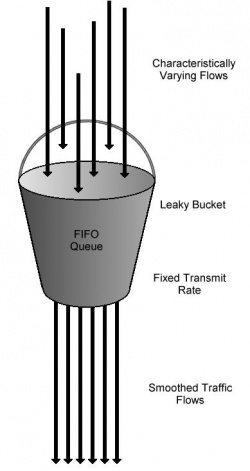
| + | A leaky bucket is a fifo buffer used to store incoming/outgoing traffic. It then leaks out packets at a set rate slowing down incoming or outgoing traffic to a desired rate. For different classes separate fifos are used to store the incoming packets. Each bucket is set to leak out packets at different rates allowing some classes to have a higher throughput than other classes. When excessive traffic causes the buffer to overflow additional incoming traffic is lost. A Random Early Discard algorithm may may use to deal with this problem. | ||
| + | |||
===Token Bucket=== | ===Token Bucket=== | ||
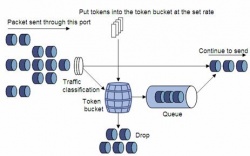
| - | A Token bucket uses tokens which are added to the bucket at a set rate r. At most n tokens can be stored in the bucket. Packets are allowed to pass through the bucket only if there are enough tokens in the bucket to allow it. Tokens are removed from the bucket as traffic is allowed to pass through. | + | A Token bucket is Similar to a Leaky bucket except that it uses tokens which are added to the bucket at a set rate r. At most n tokens can be stored in the bucket. Packets are allowed to pass through the bucket only if there are enough tokens in the bucket to allow it. Tokens are removed from the bucket as traffic is allowed to pass through. Like a Leaky Bucket Token Bucket only lets traffic through at a set rate r overall, the difference is that Token bucket allows burst speeds of up to n can occur if tokens are allowed to accumulate in the bucket. |
[[Image:Tokenbucket.jpg|thumbnail|right|250px|Token Bucket[3]]] | [[Image:Tokenbucket.jpg|thumbnail|right|250px|Token Bucket[3]]] | ||
== Costs and Benefits == | == Costs and Benefits == | ||
| - | One of the disadvantages with traffic shaping is that it usually | + | |
| + | One of the disadvantages with traffic shaping is that it usually doesn't take into account availability of network resources. Since the throughput of network traffic is fixed it won't make use of additional bandwidth if its available. | ||
| + | |||
Overflow | Overflow | ||
| - | + | Applying traffic shaping to improve network performance can be a cheaper solution than upgrading a network's hardware. | |
| - | [[Image:ShapingvsPolicing|thumbnail|right|250px|A comparison of Shaping versus Policing[2]]] | + | |
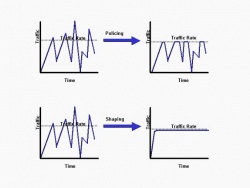
| + | Traffic shaping can also make network traffic more consistent when it tends to come in bursts. That is when traffic exceeds a set rate it is stored in a buffer. This is unlike Traffic Policing in which excessive traffic is lost. | ||
| + | [[Image:ShapingvsPolicing.jpg|thumbnail|right|250px|A comparison of Shaping versus Policing[2]]] | ||
== Uses == | == Uses == | ||
Traffic shaping is used to help manage organizations with centralized servers that are under heavy traffic. | Traffic shaping is used to help manage organizations with centralized servers that are under heavy traffic. | ||
| Line 38: | Line 42: | ||
== See Also == | == See Also == | ||
[[BitTorrent]] | [[BitTorrent]] | ||
| + | |||
==External Links== | ==External Links== | ||
| + | http://e-collection.ethbib.ethz.ch/show?type=incoll&nr=379&part=text | ||
--[[User:Younga3|Younga3]] 11:46, 9 April 2008 (EDT)Andrew Young | --[[User:Younga3|Younga3]] 11:46, 9 April 2008 (EDT)Andrew Young | ||
Revision as of 22:41, 11 April 2008
Traffic shaping (also referred to as packet shaping) is the technique of delaying and restricting certain packets traveling through a network to increase the performance of packets that have been given priority. Classes are defined to separate the packets into groupings so that they can each be shaped separately allowing some classes to pass through a network more freely than others. Traffic shapers are usually placed at the boundaries of a network to either shape the traffic going entering or leaving a network. Traffic shaping does not actually speed up a networks total thoughput. It is a tool used to help manage a network's resources.
Contents |
Implementations
Leaky bucket
A leaky bucket is a fifo buffer used to store incoming/outgoing traffic. It then leaks out packets at a set rate slowing down incoming or outgoing traffic to a desired rate. For different classes separate fifos are used to store the incoming packets. Each bucket is set to leak out packets at different rates allowing some classes to have a higher throughput than other classes. When excessive traffic causes the buffer to overflow additional incoming traffic is lost. A Random Early Discard algorithm may may use to deal with this problem.
Token Bucket
A Token bucket is Similar to a Leaky bucket except that it uses tokens which are added to the bucket at a set rate r. At most n tokens can be stored in the bucket. Packets are allowed to pass through the bucket only if there are enough tokens in the bucket to allow it. Tokens are removed from the bucket as traffic is allowed to pass through. Like a Leaky Bucket Token Bucket only lets traffic through at a set rate r overall, the difference is that Token bucket allows burst speeds of up to n can occur if tokens are allowed to accumulate in the bucket.
Costs and Benefits
One of the disadvantages with traffic shaping is that it usually doesn't take into account availability of network resources. Since the throughput of network traffic is fixed it won't make use of additional bandwidth if its available.
Overflow Applying traffic shaping to improve network performance can be a cheaper solution than upgrading a network's hardware.
Traffic shaping can also make network traffic more consistent when it tends to come in bursts. That is when traffic exceeds a set rate it is stored in a buffer. This is unlike Traffic Policing in which excessive traffic is lost.
Uses
Traffic shaping is used to help manage organizations with centralized servers that are under heavy traffic. For example ATM's are known to use the Leaky Bucket algorthm[1].
ISP's Internet Service providers will use traffic shaping increase performance of traffic that depends on good delivery times. For example packets for VoIP and gaming will in class of packets that provide a better throughput. Thus more of the limited bandwidth is made available for these packets by slowing down traffic that does not depend on latency. An example of this would be Torrents. Often users have torrents running in the background so having there traffic slowed down causes little inconvenience.
References
1. Traffic Shaping in an ATM Environment 2. http://www.cisco.com/warp/public/105/policevsshape.html 3. http://www.h3c.com/portal/Products___Solutions/Technology/QoS/QoS/200701/195599_57_0.htm 4. http://www.answers.com/topic/leaky-bucket?cat=technology
See Also
External Links
http://e-collection.ethbib.ethz.ch/show?type=incoll&nr=379&part=text
--Younga3 11:46, 9 April 2008 (EDT)Andrew Young