Conventional Encryption Algorithms
From Computing and Software Wiki
| Line 8: | Line 8: | ||
=== Monoalphabetic === | === Monoalphabetic === | ||
| - | This is a substitution technique that uses a single alphabet to replace symbols of plaintext for symbols of ciphertext as dictated by the key. These techniques are relatively easy to break due to the fact that symbol | + | This is a substitution technique that uses a single alphabet to replace symbols of plaintext for symbols of ciphertext as dictated by the key. The key often represents the number of symbols to shift the plaintext from a circular alphabet. These techniques are relatively easy to break due to the fact that symbol frequencies remain invariant. |
=== Polyalphabetic === | === Polyalphabetic === | ||
| - | === Transposition === | + | This is a substitution technique that uses multiple alphabets to replace symbols of plaintext for symbols of ciphertext as dictated by the key. The key often represents a keyword where each letter defines the alphabet being used to encrypt each symbol of the plaintext. The keyword is repeated throughout the length of the message. These techniques suppress individual symbol frequency making these ciphers harder to break. However, the keyword length determines the periodicity in which alphabets are used. This periodicity is a major vulnerability of these types of ciphers. |
| + | |||
| + | === Route Transposition === | ||
| + | This is a transposition technique where the plaintext is first written out in an mxn grid region. The key often represents a path on how to read from the grid, such as clockwise outward spiral, vertical zigzag, triangulation, etc. The ciphertext then becomes the sequence of symbols as read by the path. These techniques provide enormous amounts of available keys in which to use. However, some choices of keys are poor ones since they may leave sections of the ciphertext in their original or reversed plaintext order giving hints as to which key where used. | ||
| + | |||
| + | === Columnar Transposition === | ||
=== Synchronous Stream === | === Synchronous Stream === | ||
=== Asynchronous Stream === | === Asynchronous Stream === | ||
Revision as of 22:14, 8 April 2008
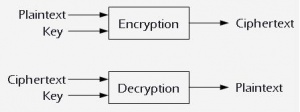
Conventional Encryption is ...
Contents |
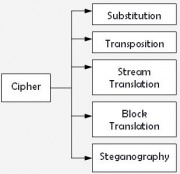
Classification of Ciphers
Monoalphabetic
This is a substitution technique that uses a single alphabet to replace symbols of plaintext for symbols of ciphertext as dictated by the key. The key often represents the number of symbols to shift the plaintext from a circular alphabet. These techniques are relatively easy to break due to the fact that symbol frequencies remain invariant.
Polyalphabetic
This is a substitution technique that uses multiple alphabets to replace symbols of plaintext for symbols of ciphertext as dictated by the key. The key often represents a keyword where each letter defines the alphabet being used to encrypt each symbol of the plaintext. The keyword is repeated throughout the length of the message. These techniques suppress individual symbol frequency making these ciphers harder to break. However, the keyword length determines the periodicity in which alphabets are used. This periodicity is a major vulnerability of these types of ciphers.
Route Transposition
This is a transposition technique where the plaintext is first written out in an mxn grid region. The key often represents a path on how to read from the grid, such as clockwise outward spiral, vertical zigzag, triangulation, etc. The ciphertext then becomes the sequence of symbols as read by the path. These techniques provide enormous amounts of available keys in which to use. However, some choices of keys are poor ones since they may leave sections of the ciphertext in their original or reversed plaintext order giving hints as to which key where used.
Columnar Transposition
Synchronous Stream
Asynchronous Stream
Steganographic
Popular Algorithms
References
[1] [2]
External Links
Elian April 8/2008